Why Your Thermostat Shouldn't Talk to Your Laptop
Network segmentation isn't just for enterprise anymore

My Cisco certifications expired years ago, but the paranoia stuck around.
When I set up my first UniFi network at home, the default was a flat network where everything talked to everything. The smart TV could see my NAS. The tablets shared a broadcast domain with my work laptop. Every IoT device had a clear path to every other device on the network.
That felt wrong. It still does.
I wrote earlier this year about why I believe in smart homes despite the security concerns. The short version: the benefits for aging in place and daily quality of life outweigh the risks, provided you manage those risks properly. Network segmentation is the foundation of that risk management.
According to Palo Alto Networks’ 2025 research, proper VLAN segmentation blocks 71% of lateral movement attempts and reduces ransomware spread by 89%. Those aren’t enterprise-only benefits. They apply to any network where you’d rather not have a compromised light bulb become a pathway to your financial documents.
What Happens on a Flat Network
The Sophos 2024 Threat Report documented something that, on flat networks, ransomware spreads to 100% of accessible systems within 4.5 hours. On segmented networks? Just 12% of systems. That’s not a marginal improvement. That’s a 733% reduction in attack surface.
Most home networks are flat by default. Your router assigns addresses from a single pool, and every device can discover and communicate with every other device. That’s convenient for Chromecast and AirPlay. It’s also convenient for malware.
I’ve seen firsthand how quickly things can go sideways. A friend’s network got hit because a cheap IP camera with a known vulnerability became the entry point. Within hours, the attacker had pivoted to the NAS and personal files. The camera and the NAS had no business talking to each other. On a segmented network, they wouldn’t have been able to.
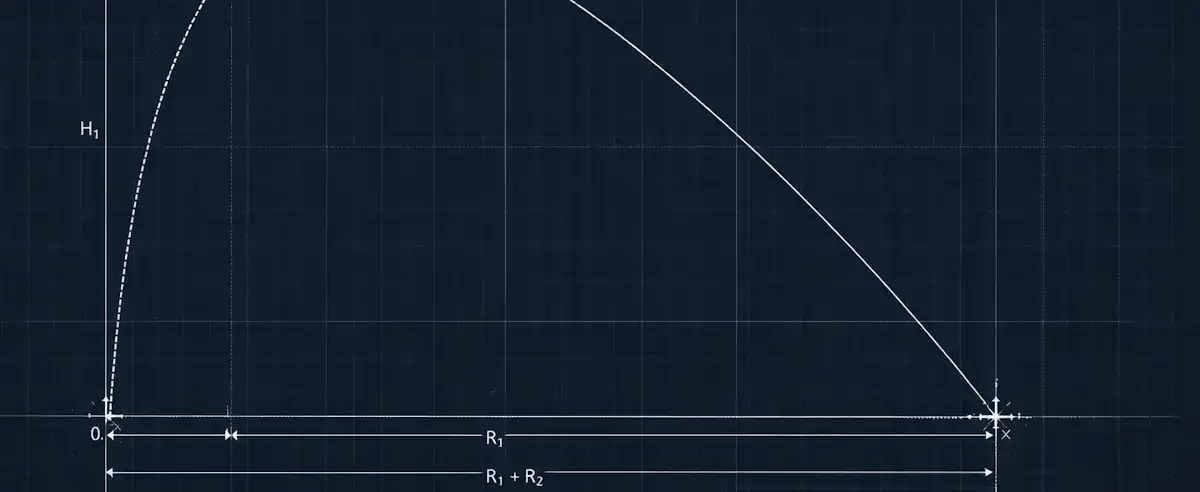
Flat vs. Segmented Network Impact
Sources: Sophos 2024 Threat Report, Palo Alto Networks 2025
The VLAN Structure That Works for Me
After experimenting with various configurations, I settled on a structure that balances security with the reality that smart home devices need to actually function. The 802.1Q standard gives you up to 4,094 VLANs per domain, but for a home network, you really only need a handful.
Trusted VLAN (VLAN 10): Personal devices that need full network access. Laptops, phones, tablets, and anything else I actually trust. These devices can initiate connections to other VLANs when needed, but nothing initiates connections back to them.
IoT VLAN (VLAN 20): The quarantine zone. Smart speakers, thermostats, light bulbs, robot vacuums. These devices get internet access for cloud services and firmware updates, but they can’t see or reach anything else on my network. If one gets compromised, the blast radius is contained.
Camera VLAN (VLAN 30): Security cameras get their own segment. They talk to my NVR (which is on this VLAN) and nowhere else. No cloud access unless I explicitly allow it for specific devices.
Services VLAN (VLAN 40): Public servers for projects I host. These devices need to be accessible from the internet, but they can’t see or reach anything else on my network. If one gets compromised, the blast radius is contained.
Guest VLAN (VLAN 50): Exactly what it sounds like. Internet access only. Complete isolation from everything internal. I don’t need to worry about what’s on a visitor’s phone.
The Catch: VLANs Aren’t Enough
This is where I see a lot of homelab guides get it wrong. They stop at VLAN creation and assume the job is done. VLANs segment traffic at Layer 2, but without firewall rules, traffic can still route between VLANs through your gateway.
Creating a VLAN is step one. Configuring inter-VLAN firewall rules is where the actual security happens.
My default rule is simple: deny all inter-VLAN traffic, then add specific exceptions. The IoT VLAN can reach the internet. It cannot reach my Trusted VLAN. Period. If I need my phone to control a smart device, I either use the cloud service (which routes through the internet anyway) or I create a specific allow rule for that device’s control port.
Basic Firewall Rule Structure
Rule 1: Allow Trusted → Any (established, related)
Rule 2: Allow IoT → Internet only
Rule 3: Allow Camera → NVR only
Rule 3: Allow Services → Internet only (locked to ports)
Rule 4: Allow Guest → Internet only
Rule 5: Deny all inter-VLAN (default)
Order matters. Rules evaluate top-down until a match is found. The deny rule goes last—it catches everything the allows didn't match.
Making Smart Home Features Actually Work
The tricky part is that smart home devices often rely on multicast protocols for discovery. Chromecast uses mDNS. HomeKit uses Bonjour. If you completely isolate your IoT VLAN, your phone on the Trusted VLAN won’t discover devices on the IoT VLAN.
Two settings saved me hours of troubleshooting:
IGMP Snooping: Enable this on your switch. It optimizes multicast traffic delivery so your network doesn’t flood every port with multicast packets. Most managed switches support this, including UniFi.
mDNS Reflector/Repeater: This allows multicast DNS traffic to cross VLAN boundaries for discovery purposes without opening full connectivity. UniFi has this built in. Firewalla calls it “mDNS reflection.” The specific name varies, but the concept is the same: let devices discover each other without letting them communicate freely.
The Maintenance Nobody Talks About
Setting up VLANs is a weekend project. Maintaining them is ongoing. Every new device needs to be assigned to the right VLAN. Every firmware update could change a device’s network requirements. Every new integration might need a new firewall rule.
I keep a Google Sheet. Device name, MAC address, assigned VLAN, static IP (for critical devices), and notes on any special firewall rules. It’s not glamorous, but when something breaks at 10pm and I need to troubleshoot, having documentation beats trying to remember what I configured six months ago.
The other maintenance task that matters: firmware updates. Zscaler’s ThreatLabz research documented a 400% year-over-year increase in OT/IoT attacks. The single most effective defense is keeping firmware current. I check quarterly at minimum, and I’ve set up notifications where supported.
Is This Worth the Effort?
For me, yes. The peace of mind knowing that my smart light bulbs can’t become a pathway to my work files is worth the initial setup time and ongoing maintenance.
But I’ll be honest: this isn’t for everyone. If you’re running a basic home network with a few devices and minimal risk exposure, the default flat network might be fine. The complexity of VLAN management has a cost, and that cost needs to be weighed against the actual threat model you’re facing.
My threat model includes: work-from-home with access to company resources, a NAS with irreplaceable family photos and archives, and a home lab of various experiments, prototype projects, and consulting work shared with clients. Given that model, segmentation is non-negotiable.
Your threat model might be different. The question isn’t whether VLANs are universally necessary. It’s whether the attack surface you’re currently exposing matches the risk you’re willing to accept.
I’d rather spend a weekend configuring firewall rules than spend weeks recovering from a breach that proper segmentation would have prevented.